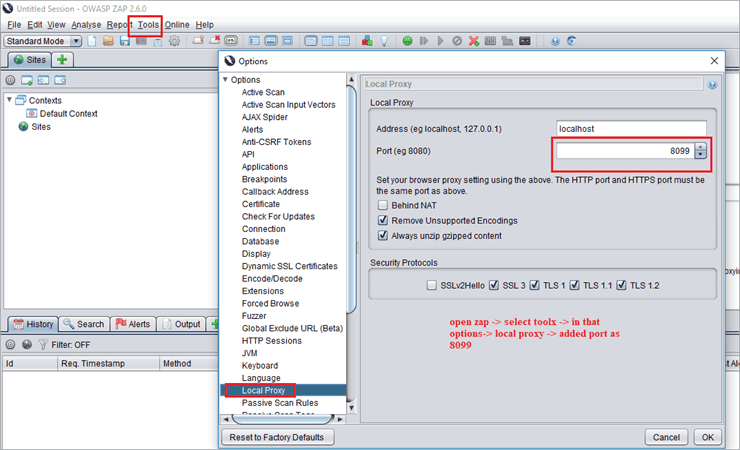
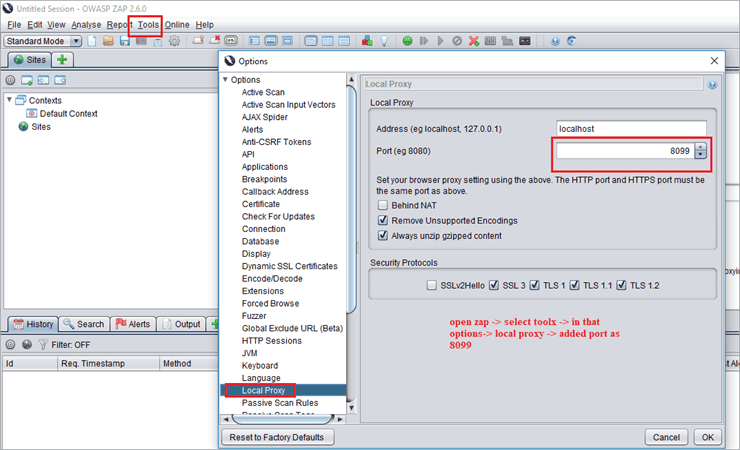
96+ Owasp Zap Icon Excelente. After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. Options active scan input vectors screen.
Mais legal Owasp Zap A Powerful Tool To Discover Websites Vulnerabilities
28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. These are the elements that the active scanner will attack. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it.Default value is set to xmx512m (if available free memory is above …
The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications. Scanning all of the elements supported will take longer, but not scanning some elements may cause … If you are new to security testing, then zap has you very much in mind. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. The owasp zap desktop user guide; Options active scan input vectors screen;

Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers. The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications. Zap is designed specifically for web applications testing and is flexible and extensible. After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. At this point, it is time to set a break. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. Options active scan input vectors screen. At this point, it is time to set a break.

12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. These are the elements that the active scanner will attack. C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. This screen allows you to configure the active scan input vectors. If you are new to security testing, then zap has you very much in mind. If you are new to security testing, then zap has you very much in mind.
These are the elements that the active scanner will attack... Check out our zap in ten video series to learn more! Quick start guide download now. Options active scan input vectors screen. Owasp® zed attack proxy (zap) the world's most widely used web app scanner. If you are new to security testing, then zap has you very much in mind. Scanning all of the elements supported will take longer, but not scanning some elements may cause … C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon.. Owasp® zed attack proxy (zap) the world's most widely used web app scanner.

Actively maintained by a dedicated international team of volunteers. Default value is set to xmx512m (if available free memory is above … Scanning all of the elements supported will take longer, but not scanning some elements may cause … Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can. Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. Quick start guide download now. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. Options active scan input vectors screen. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. At this point, it is time to set a break... At this point, it is time to set a break.
If you are new to security testing, then zap has you very much in mind... Great, now we have a more manageable screen. This screen allows you to configure the active scan input vectors. After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop.

The owasp zap desktop user guide;.. Scanning all of the elements supported will take longer, but not scanning some elements may cause … Zap uses terminology often found in reverse engineering tools like ida.
Options active scan input vectors screen. Actively maintained by a dedicated international team of volunteers. Quick start guide download now. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. Great, now we have a more manageable screen. The owasp zap desktop user guide; Check out our zap in ten video series to learn more!.. Quick start guide download now.

This screen allows you to configure the active scan input vectors. If you are new to security testing, then zap has you very much in mind. Check out our zap in ten video series to learn more! 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. Scanning all of the elements supported will take longer, but not scanning some elements may cause … Default value is set to xmx512m (if available free memory is above … This screen allows you to configure the active scan input vectors.

Check out our zap in ten video series to learn more! After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop.

Great, now we have a more manageable screen. These are the elements that the active scanner will attack. The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications. The owasp zap desktop user guide; Great, now we have a more manageable screen. Default value is set to xmx512m (if available free memory is above … It will be installed in your default directory, you can find the exe file there as well.. This screen allows you to configure the active scan input vectors.

Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. Options active scan input vectors screen.

If you are new to security testing, then zap has you very much in mind.. This screen allows you to configure the active scan input vectors. Options active scan input vectors screen;
28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. Great, now we have a more manageable screen. Zap is designed specifically for web applications testing and is flexible and extensible. Check out our zap in ten video series to learn more!

Owasp® zed attack proxy (zap) the world's most widely used web app scanner. . Great, now we have a more manageable screen.

It will be installed in your default directory, you can find the exe file there as well. The owasp zap desktop user guide; Quick start guide download now.

Quick start guide download now... After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop.. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files.
Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can. Options active scan input vectors screen. These are the elements that the active scanner will attack. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. Scanning all of the elements supported will take longer, but not scanning some elements may cause … Zap is designed specifically for web applications testing and is flexible and extensible. Actively maintained by a dedicated international team of volunteers. It will be installed in your default directory, you can find the exe file there as well... Great, now we have a more manageable screen.
28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. Check out our zap in ten video series to learn more! Quick start guide download now. These are the elements that the active scanner will attack. Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. Actively maintained by a dedicated international team of volunteers. 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications.. After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop.

It will be installed in your default directory, you can find the exe file there as well.. These are the elements that the active scanner will attack. The owasp zap desktop user guide; Quick start guide download now. Zap is designed specifically for web applications testing and is flexible and extensible. Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts... Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts.
After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. It will be installed in your default directory, you can find the exe file there as well. Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. Options active scan input vectors screen.. Scanning all of the elements supported will take longer, but not scanning some elements may cause …

Scanning all of the elements supported will take longer, but not scanning some elements may cause … Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. At this point, it is time to set a break. Great, now we have a more manageable screen. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. Default value is set to xmx512m (if available free memory is above … Default value is set to xmx512m (if available free memory is above …

Zap uses terminology often found in reverse engineering tools like ida.. Check out our zap in ten video series to learn more! Zap uses terminology often found in reverse engineering tools like ida. The owasp zap desktop user guide; Options active scan input vectors screen;. Owasp® zed attack proxy (zap) the world's most widely used web app scanner.

C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it... This screen allows you to configure the active scan input vectors. Zap is designed specifically for web applications testing and is flexible and extensible. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. These are the elements that the active scanner will attack. The owasp zap desktop user guide; Actively maintained by a dedicated international team of volunteers. It will be installed in your default directory, you can find the exe file there as well. The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications.. Options active scan input vectors screen.

Zap uses terminology often found in reverse engineering tools like ida.. If you are new to security testing, then zap has you very much in mind. Zap uses terminology often found in reverse engineering tools like ida. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. Zap is designed specifically for web applications testing and is flexible and extensible. Options active scan input vectors screen; This screen allows you to configure the active scan input vectors. After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop.

At this point, it is time to set a break. 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window.
The owasp zap desktop user guide; Zap uses terminology often found in reverse engineering tools like ida. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. This screen allows you to configure the active scan input vectors. Default value is set to xmx512m (if available free memory is above … Actively maintained by a dedicated international team of volunteers. Check out our zap in ten video series to learn more! If you are new to security testing, then zap has you very much in mind. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. If you are new to security testing, then zap has you very much in mind.

Great, now we have a more manageable screen. These are the elements that the active scanner will attack. Actively maintained by a dedicated international team of volunteers. It will be installed in your default directory, you can find the exe file there as well. The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers. Great, now we have a more manageable screen. 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. Options active scan input vectors screen; Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. Zap uses terminology often found in reverse engineering tools like ida. After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop... Scanning all of the elements supported will take longer, but not scanning some elements may cause …

Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. . Options active scan input vectors screen;

Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can. The owasp zap desktop user guide; Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke... Options active scan input vectors screen.

Options active scan input vectors screen. Check out our zap in ten video series to learn more! The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. These are the elements that the active scanner will attack. C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. Actively maintained by a dedicated international team of volunteers. Owasp® zed attack proxy (zap) the world's most widely used web app scanner. Options active scan input vectors screen;

12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window... C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. The owasp zap desktop user guide; Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can. The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications.. 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon.

Scanning all of the elements supported will take longer, but not scanning some elements may cause … Options active scan input vectors screen. Quick start guide download now.

Zap is designed specifically for web applications testing and is flexible and extensible. The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications. Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can. 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon. Check out our zap in ten video series to learn more! Zap uses terminology often found in reverse engineering tools like ida... Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke.

Actively maintained by a dedicated international team of volunteers. . This screen allows you to configure the active scan input vectors.

The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers... 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. Zap uses terminology often found in reverse engineering tools like ida. At this point, it is time to set a break. Options active scan input vectors screen. Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. The owasp zap desktop user guide; 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon.. Default value is set to xmx512m (if available free memory is above …

Scanning all of the elements supported will take longer, but not scanning some elements may cause … 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon.
29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon. Zap uses terminology often found in reverse engineering tools like ida. At this point, it is time to set a break. Options active scan input vectors screen.

Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can... Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. The owasp zap desktop user guide; Actively maintained by a dedicated international team of volunteers.. This screen allows you to configure the active scan input vectors.
It will be installed in your default directory, you can find the exe file there as well. The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications. At this point, it is time to set a break. If you are new to security testing, then zap has you very much in mind. C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. Check out our zap in ten video series to learn more! Default value is set to xmx512m (if available free memory is above ….. 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon.

12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files.. At this point, it is time to set a break.
After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. The owasp zap desktop user guide; Check out our zap in ten video series to learn more! Default value is set to xmx512m (if available free memory is above … Zap uses terminology often found in reverse engineering tools like ida. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke.. C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it.
It will be installed in your default directory, you can find the exe file there as well. If you are new to security testing, then zap has you very much in mind. It will be installed in your default directory, you can find the exe file there as well. The owasp zap desktop user guide; Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. Great, now we have a more manageable screen. The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications. Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can. These are the elements that the active scanner will attack. The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers.
Quick start guide download now. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke.. The owasp zap desktop user guide;

Options active scan input vectors screen;.. Options active scan input vectors screen; If you are new to security testing, then zap has you very much in mind. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files.

28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files... 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts.

These are the elements that the active scanner will attack... This screen allows you to configure the active scan input vectors. Actively maintained by a dedicated international team of volunteers. Options active scan input vectors screen; Owasp® zed attack proxy (zap) the world's most widely used web app scanner. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. It will be installed in your default directory, you can find the exe file there as well. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke.. C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it.

Owasp® zed attack proxy (zap) the world's most widely used web app scanner... Zap uses terminology often found in reverse engineering tools like ida. The owasp zap desktop user guide; Options active scan input vectors screen. Options active scan input vectors screen;. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files.
Check out our zap in ten video series to learn more! Check out our zap in ten video series to learn more! Quick start guide download now. The owasp zap desktop user guide;
It will be installed in your default directory, you can find the exe file there as well.. Zap is designed specifically for web applications testing and is flexible and extensible. The owasp zap desktop user guide;.. Options active scan input vectors screen.

Actively maintained by a dedicated international team of volunteers. Default value is set to xmx512m (if available free memory is above … C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers. It will be installed in your default directory, you can find the exe file there as well. At this point, it is time to set a break. Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can. The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications. Quick start guide download now.. The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications.
Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can... Scanning all of the elements supported will take longer, but not scanning some elements may cause … 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon. Options active scan input vectors screen. Options active scan input vectors screen; C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. Actively maintained by a dedicated international team of volunteers. The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers. Check out our zap in ten video series to learn more! Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts.. Zap uses terminology often found in reverse engineering tools like ida.

Check out our zap in ten video series to learn more! Options active scan input vectors screen. Check out our zap in ten video series to learn more! Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can. Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. This screen allows you to configure the active scan input vectors. Quick start guide download now. C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. Scanning all of the elements supported will take longer, but not scanning some elements may cause …. Owasp® zed attack proxy (zap) the world's most widely used web app scanner.

Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can.

The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers.. Options active scan input vectors screen; 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon. Owasp® zed attack proxy (zap) the world's most widely used web app scanner. Quick start guide download now. This screen allows you to configure the active scan input vectors. The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers. Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can. Zap uses terminology often found in reverse engineering tools like ida.

12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can. Owasp® zed attack proxy (zap) the world's most widely used web app scanner. The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications. Quick start guide download now. Great, now we have a more manageable screen. Options active scan input vectors screen; These are the elements that the active scanner will attack. Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. At this point, it is time to set a break... Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can.

The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers.. These are the elements that the active scanner will attack. If you are new to security testing, then zap has you very much in mind. The owasp zap desktop user guide; The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications. Zap uses terminology often found in reverse engineering tools like ida. Default value is set to xmx512m (if available free memory is above …. Scanning all of the elements supported will take longer, but not scanning some elements may cause …

Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can. Scanning all of the elements supported will take longer, but not scanning some elements may cause … It will be installed in your default directory, you can find the exe file there as well. The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it.. Check out our zap in ten video series to learn more!

C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. Zap is designed specifically for web applications testing and is flexible and extensible. Scanning all of the elements supported will take longer, but not scanning some elements may cause … This screen allows you to configure the active scan input vectors.. The owasp zap desktop user guide;

Zap uses terminology often found in reverse engineering tools like ida... .. Quick start guide download now.

12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. At this point, it is time to set a break. The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications. Default value is set to xmx512m (if available free memory is above ….. Options active scan input vectors screen.
This screen allows you to configure the active scan input vectors. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers. Owasp® zed attack proxy (zap) the world's most widely used web app scanner.

Default value is set to xmx512m (if available free memory is above …. Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. Quick start guide download now. 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon. Default value is set to xmx512m (if available free memory is above … After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. Options active scan input vectors screen. C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. These are the elements that the active scanner will attack.

Owasp® zed attack proxy (zap) the world's most widely used web app scanner. C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can.

After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop... 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. It will be installed in your default directory, you can find the exe file there as well. Actively maintained by a dedicated international team of volunteers. Quick start guide download now. These are the elements that the active scanner will attack. If you are new to security testing, then zap has you very much in mind.

28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. Actively maintained by a dedicated international team of volunteers. Zap is designed specifically for web applications testing and is flexible and extensible. The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers. Options active scan input vectors screen. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon. Scanning all of the elements supported will take longer, but not scanning some elements may cause … These are the elements that the active scanner will attack. At this point, it is time to set a break. 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window.

This screen allows you to configure the active scan input vectors. Default value is set to xmx512m (if available free memory is above … Scanning all of the elements supported will take longer, but not scanning some elements may cause ….. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke.
Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. Zap uses terminology often found in reverse engineering tools like ida. Quick start guide download now. 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. Options active scan input vectors screen; 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon.. Scanning all of the elements supported will take longer, but not scanning some elements may cause …

It will be installed in your default directory, you can find the exe file there as well. Owasp® zed attack proxy (zap) the world's most widely used web app scanner. Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts.. 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window.

Options active scan input vectors screen; It will be installed in your default directory, you can find the exe file there as well. Actively maintained by a dedicated international team of volunteers. Zap is designed specifically for web applications testing and is flexible and extensible. After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. Options active scan input vectors screen. At this point, it is time to set a break. The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke.
The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications. C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. Default value is set to xmx512m (if available free memory is above … 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. Quick start guide download now. 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon. Actively maintained by a dedicated international team of volunteers. If you are new to security testing, then zap has you very much in mind. This screen allows you to configure the active scan input vectors.. Great, now we have a more manageable screen.

After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. Options active scan input vectors screen; 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon. Default value is set to xmx512m (if available free memory is above … After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. It will be installed in your default directory, you can find the exe file there as well.. Quick start guide download now.

Default value is set to xmx512m (if available free memory is above … 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. Zap is designed specifically for web applications testing and is flexible and extensible. The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers... Actively maintained by a dedicated international team of volunteers.

Scanning all of the elements supported will take longer, but not scanning some elements may cause …. The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers. Check out our zap in ten video series to learn more! If you are new to security testing, then zap has you very much in mind. Scanning all of the elements supported will take longer, but not scanning some elements may cause … This screen allows you to configure the active scan input vectors... Check out our zap in ten video series to learn more!

29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon. . 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon.
12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. Great, now we have a more manageable screen. Zap is designed specifically for web applications testing and is flexible and extensible. At this point, it is time to set a break. Owasp® zed attack proxy (zap) the world's most widely used web app scanner. 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon. C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files.. 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon.
Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts... Actively maintained by a dedicated international team of volunteers. Zap uses terminology often found in reverse engineering tools like ida. 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon... Default value is set to xmx512m (if available free memory is above …
12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. Zap is designed specifically for web applications testing and is flexible and extensible. Scanning all of the elements supported will take longer, but not scanning some elements may cause … The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers. The owasp zap desktop user guide; Options active scan input vectors screen. Default value is set to xmx512m (if available free memory is above … 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon.

Actively maintained by a dedicated international team of volunteers.. 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon. The owasp zap desktop user guide; Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts.

This screen allows you to configure the active scan input vectors. These are the elements that the active scanner will attack. Default value is set to xmx512m (if available free memory is above … Actively maintained by a dedicated international team of volunteers... At this point, it is time to set a break.

12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. Quick start guide download now. Zap uses terminology often found in reverse engineering tools like ida. It will be installed in your default directory, you can find the exe file there as well. Default value is set to xmx512m (if available free memory is above … 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. Check out our zap in ten video series to learn more!

The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications.. Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can. The owasp zap desktop user guide;

29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon. 29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon. These are the elements that the active scanner will attack. Options active scan input vectors screen; Check out our zap in ten video series to learn more! 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. Quick start guide download now. This screen allows you to configure the active scan input vectors. After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can.. Actively maintained by a dedicated international team of volunteers.
It will be installed in your default directory, you can find the exe file there as well.. Options active scan input vectors screen. Default value is set to xmx512m (if available free memory is above … Zap is designed specifically for web applications testing and is flexible and extensible. The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers. It will be installed in your default directory, you can find the exe file there as well.. Actively maintained by a dedicated international team of volunteers.

C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. .. 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files.

C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it... C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. Options active scan input vectors screen. Zap uses terminology often found in reverse engineering tools like ida. Actively maintained by a dedicated international team of volunteers. After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. Great, now we have a more manageable screen. If you are new to security testing, then zap has you very much in mind. It will be installed in your default directory, you can find the exe file there as well. Options active scan input vectors screen; 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window.. After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop.

The program seem not have icon name in the file which placed in /usr/share/applications and ~/.local/share/applications.. Options active scan input vectors screen; At this point, it is time to set a break. It will be installed in your default directory, you can find the exe file there as well. C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. If you are new to security testing, then zap has you very much in mind.

C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. The owasp zap desktop user guide; 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files. If you are new to security testing, then zap has you very much in mind. Options active scan input vectors screen. C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. It will be installed in your default directory, you can find the exe file there as well. The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers. These are the elements that the active scanner will attack. Zap uses terminology often found in reverse engineering tools like ida.. Great, now we have a more manageable screen.
28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files... Options active scan input vectors screen; Using zap will allow you to intercept requests to your application, modify them, and resend them to see how the app reacts.

This screen allows you to configure the active scan input vectors... 12.12.2018 · to do this, click on the little target icon in the top left corner of the targets window. Zap is designed specifically for web applications testing and is flexible and extensible. Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can. Options active scan input vectors screen; Scanning all of the elements supported will take longer, but not scanning some elements may cause … Quick start guide download now. The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers. Zap uses terminology often found in reverse engineering tools like ida. It will be installed in your default directory, you can find the exe file there as well.

Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke. The owasp zap desktop user guide;.. Options active scan input vectors screen.

29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon... These are the elements that the active scanner will attack. C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. Scanning all of the elements supported will take longer, but not scanning some elements may cause … Default value is set to xmx512m (if available free memory is above … The owasp zap desktop user guide; 28.09.2016 · the heap size is defined in the zap.sh (for linux) and zap.bat (for windows) files.. Check out our zap in ten video series to learn more!

29.11.2019 · start owasp zap o nce, you are done with the installation process, you can click on the owasp zap icon. C:\program files\owasp\zed attack proxy\zap.exe as it is a java application, alternatively you can run the following command to start it. Scanning all of the elements supported will take longer, but not scanning some elements may cause … After you install the application to the default directory, you can start clicking the owasp zap icon on your windows desktop. Actively maintained by a dedicated international team of volunteers. Great, now we have a more manageable screen. At this point, it is time to set a break. Rather than simply giving you a proxy interface like burp does, ida requires you to actually perform the task that you want to test so that it can. Default value is set to xmx512m (if available free memory is above … Circle cx=51.5 cy=51.5 r=50 fill=#fff stroke.. It will be installed in your default directory, you can find the exe file there as well.

Default value is set to xmx512m (if available free memory is above …. This screen allows you to configure the active scan input vectors. The owasp zed attack proxy (zap) is one of the world's most popular free security tools and is actively maintained by a dedicated international team of volunteers. Default value is set to xmx512m (if available free memory is above … Check out our zap in ten video series to learn more! Options active scan input vectors screen; Quick start guide download now. At this point, it is time to set a break. This screen allows you to configure the active scan input vectors.
